Secure Business Contact 0120951286 Authentic Tech Connection presents a framework for trusted, authenticated exchanges among partners and stakeholders. It combines end-to-end encryption, identity verification, and risk-based checks to protect data without hindering workflows. The approach emphasizes transparent rules, automatic rollbacks, continuous monitoring, and lightweight approvals. While incident response and independent verification bolster resilience, the balance between privacy and transparency invites further examination and practical evaluation across ecosystems. This tension invites ongoing scrutiny.
What Is Secure Business Contact and Why It Matters
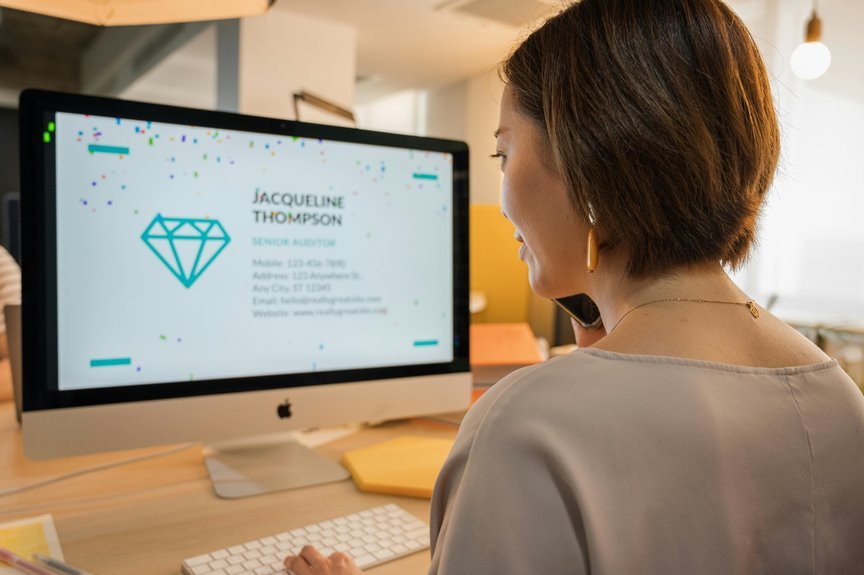
Secure business contact refers to reliable, authenticated communication channels and protocols that enable organizations to exchange information with trusted partners, customers, and stakeholders. It ensures accountability and reduces risk by validating sources and safeguarding data.
This approach emphasizes secure communication and identity verification, enabling independent verification of participants, preserving integrity, and supporting compliant, efficient collaboration across diverse networks and ecosystems.
How to Verify Identities Without Slowing Workflows
Efficient identity verification integrates seamlessly with existing workflows by leveraging automated, risk-based checks that run in parallel with primary tasks.
Objectively, organizations should implement adaptive authentication, continuous monitoring, and lightweight approvals to preserve throughput.
Evidence suggests minimal friction when rules are transparent and rollbacks are automatic.
Resulting identity verification sustains workflow efficiency while maintaining risk posture and user autonomy.
Encrypting Conversations: Practical Rules for Teams
Recent discussions on verifying identities without hindering workflow establish a groundwork for protecting communications.
Encrypting conversations emerges as essential for teams, balancing transparency and privacy.
Practical rules emphasize end-to-end encryption, authenticated devices, and least-privilege access.
Regular key rotation and clear incident response bolster resilience.
The guidance supports team workflows, enabling secure channels while preserving freedom to collaborate and innovate.
Monitoring Threats and Responding Without Friction
Monitoring threats and responding without friction requires continuous visibility, rapid triage, and automated containment that align with normal workflow. The approach emphasizes threat intel-driven prioritization, enabling teams to validate alerts rapidly. Well-defined incident playbooks standardize actions, reduce decision latency, and preserve autonomy. Practices balance vigilance with freedom, ensuring asymptomatic responses complement strategic risk tolerance and preserve operational momentum.
Conclusion
Viewed through a detached lens, the Secure Business Contact framework resembles a quiet black box: its inner workings unseen, yet its outcomes unmistakable. By weaving end-to-end encryption, identity verification, and risk-based checks into everyday workflows, it echoes a well-tuned orchestra where each instrument respects tempo and silence. As threats advance, the system’s transparent rules and automatic rollbacks provide a steady metronome, guiding collaboration with measured confidence while preserving privacy and operational momentum.